AWS CloudWatch Logs Simplified
Sat, Jun 15, 2024
Amazon CloudWatch is a powerful monitoring and observability service from AWS. However, inspecting logs via AWS Management Console in a browser is far from a pleasant experience. Therefore, I have developed a small bash script that simplifies logging inspection.
In order to run aws commands in terminal you need to have the AWS CLI installed and configured with appropriate AWS credentials and permissions. To follow the steps below, you should be familiar with how to create and execute a shell script.
#!/bin/bash
# PS3 is a shell variable in Bash that defines the prompt string displayed to the user when using the select command
PS3="Select a log group: "
# add the names of the CloudWatch log groups you want to tail with this script
options=(
"api.hackerstore"
"cognito.hackerstore"
"lambda.hackerstore"
"Quit"
)
# $COLUMNS is an environment variable that holds the number of columns (width) of the terminal window.
# set COLUMNS to a small value to force vertical display.
# this environment variable is local to the shell instance running the script.
# when the script exits, the original shell environment remains unaffected by changes made within the script, so no need to reset.
export COLUMNS=1
# start select loop to choose a log group
select choice in "${options[@]}"; do
case $choice in
# If "api.hackerstore" is selected, tail the corresponding CloudWatch logs
"api.hackerstore")
# aws logs tail <replace with your log group name> --follow
aws logs tail /aws/apigateway/hackerstore --follow # --follow to continuously stream new log events to the console as they become available
;;
# If "cognito.hackerstore" is selected, tail the corresponding CloudWatch logs
"cognito.hackerstore")
aws logs tail /aws/cognito/hackerstore --follow
;;
# If "lambda.hackerstore" is selected, tail the corresponding CloudWatch logs
"lambda.hackerstore")
aws logs tail aws/lambda/hackerstore --follow
;;
# If "Quit" is selected, exit the script
"Quit")
echo "Exiting script."
break
;;
# If an invalid option is selected, display an error message
*)
echo "Invalid option. Please choose a number or Quit."
;;
esac
done
AWS log group names are generated by AWS when a resource is created and can be viewed in the AWS console. If you are using AWS CDK to define your cloud resources, you can define a custom log group name.
const api = new cdk.aws_apigateway.RestApi(this, `hackerstoreapi`, {
deployOptions: {
loggingLevel: cdk.aws_apigateway.MethodLoggingLevel.INFO,
accessLogDestination: new cdk.aws_apigateway.LogGroupLogDestination(new cdk.aws_logs.LogGroup(this, `hackerstoreapilogs`, {
logGroupName: `<define your custom log group name here>`,
retention: cdk.aws_logs.RetentionDays.INFINITY,
removalPolicy: cdk.RemovalPolicy.RETAIN
}))
}
});
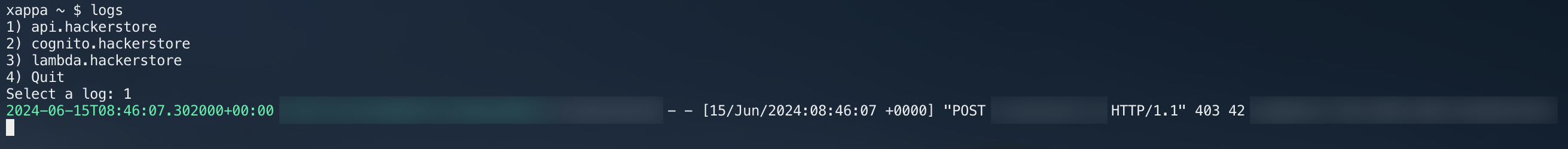
Script in action.